LSE Summer Week - July 15 - July 18 2015
Lieu et plan d'accès
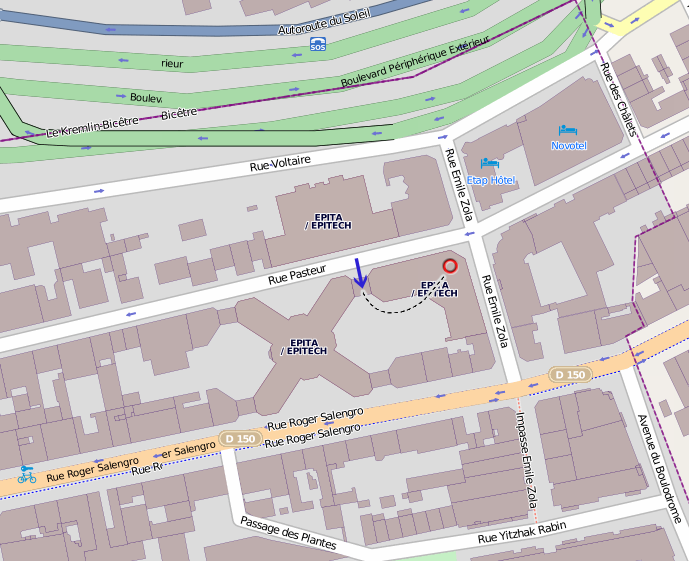
Amphithéâtre 4, EPITA, 24 rue Pasteur, 94276 Le Kremlin-Bicêtre.
Transports en commun : métro 7 (station Porte d'Italie), bus 47/125/131/185/186 (station Roger Salengro-Fontainebleau).
Planning Complet
Wednesday 15
Introducing the LSE Week
19h15 19h30
RCU: Theory and Practice - Marwan Burelle
19h30 20h30Short introduction to RCU algorithms looking at concrete RCU implementations (user and/or kernel land), the various strategies and their impact on performances (the overhead on reader and writers, etc.), Slides Youtube
Open source toolchain for FPGA - Vincent Gatine
20h30 21h30Discovery of an open toolchain made for FPGA synthesis based on yosys, arachne-pnr and the icestorm projects. This talk will cover various aspects of FPGA programming from synthesis to reverse-engineering bitstreams. Slides Youtube
What's new in STOS - Gabriel Laskar & Jérémy Lefaure
21h30 22h30STOS, our in-house kernel, has seen many changes this year. Here is a presentation of what changed, what's new, and what we are planning to do for the next year. Slides Youtube
Thursday 16
Pyrser Selectors Langage - Lionel Auroux
19h30 20h30AST handling makes the understanding of language semantic very difficult. The pyrser toolbox implements it in a new way, matching and rewriting AST patterns. Pyrser selectors allow us to describe patterns of trees through a little language, and handle them. The use of PSL makes semantics easy to find and read. Here is an explanation of how PSL works based on bottom-up tree automata. Slides Youtube
Linux boot protocol - Nassim Eddequiouaq
20h30 21h30A deep insight into the x86 Linux kernel boot process. On Intel x86, how to go from early kernel loading to the end of initialization and the launch of the init program. Slides Youtube
Virtio on early kernels - Nahim El Atmani
21h30 22h30Enabling virtual devices for virtual machines, virtio presents many challenges and advantages during realization. Here is a presentation of how virtio works and the implementation process in a new kernel Slides Youtube
Friday 17
Primality Tests and Factoring with the AKS polynomials - Robert Erra
19h30 20h30Prime numbers are ubiquitous in modern cryptography and fortunately a lot of probabilistic and deterministic primality tests exist. The most famous is the AKS algorithm that has proved that “Prime is in P”, a result that has is one of the most important results in the last 30 years in computational number theory. On the other side, Factoring a large number is a hard problem whose complexity is still unknown. We propose here to analyse the following question: if we take a composite number what information can we obtain with primality tests ? We will explain how in some cases we can factor a number using primality tests ; we will for example explain why Charmichael numbers are easy to factor and we will finish with the presentation of a new (and curious) factorization algorithm that use the AKS polynomials, the algorithm is not efficient but it is deterministic and can still be improved. Slides Youtube
Draw me a Windows local kernel debugger - Samuel Chevet & Clément Rouault
20h30 21h30Our journey to automatize some local kernel debugging without the use of Windbg. We will explain how dbgengine (core of Windbg) works: which API are exposed and what does it require to work properly. Finally, we will show how to abuse it to be able to perform local kernel debugging in Python.
Execution trace and memory analysis - Matthieu Tardy
21h30 22h30When reverse engineering, optimizing, or debugging a binary, one could often use an overview of the changes happening in memory. This talk will introduce a memory analysis tool based on pin, cover how this tool is implemented and show some of its use cases. Slides Youtube
Saturday 18
When the Exponent Matters - Marwan Burelle
13h00 13h30Graph diameters for big (more than 100000 vertices) real-life, unoriented and unvaluated sparse graphs are not tractable due to N³/N² complexity. This talk will introduce some strategies used to reduce the amount of computation needed to find diameter in such cases. Slides Youtube
Subverting the C++ compiler - Gabriel Laskar
13h30 14h00When performance matters, and coding standards don't. A glimpse of a world in which you try to bend the c++ compiler to your will. Slides Youtube
Early PC architecture - Rémi Audebert
14h00 15h00How do IBM PCs work ? From the CPU and RAM to the devices and peripherals, these long since retired systems still live where backward-compatibility is required. This talk will explain how each component of these systems interacts with each other and give a good understanding of how computers work. Slides Youtube
Introducing the LSE-PC - Pierre Surply
15h00 16h00The LSE-PC aims to be a compact IBM-PC compatible development board based on an Intel 80386SX CPU and an Altera Cyclone IV FPGA in order to emulate a custom chipset. This presentation will focus on how we have developed this motherboard from scratch, explaining the lessons learned and its expected applications. Slides Youtube
Linux Rootkit - Adrien Schildknecht
16h00 17h00Let's have some fun with a Linux and a x86 CPU. This talk explains some of the advanced features of modern x86 CPUs and how to use them against a running Linux kernel (sysenter, syscall, debug registers, lbr…) Slides Youtube
Striptease of the Android permissions system - Alizée Penel
17h00 18h00Throughout this talk, we are going to present how the Android permission system is implemented, all the way from the kernel to the application layer. Next, we will demonstrate a use case of an Android application which leads to a huge security hole, then fix it. Slides Youtube
Cheating in online video-game: An example with CS:GO - Adrien Garin
18h00 19h00Today, most famous video-games come with anti-cheat software, like VAC for Valve games. How do they behave? What are the methods used by cheaters to bypass detection and cheat safely? This talk is an overview of code injection techniques and hooking in Windows with a practical example: A CS:GO cheat. Slides Youtube
Barbecue
20h00