LSE Winter Days November 6 - November 7 2021
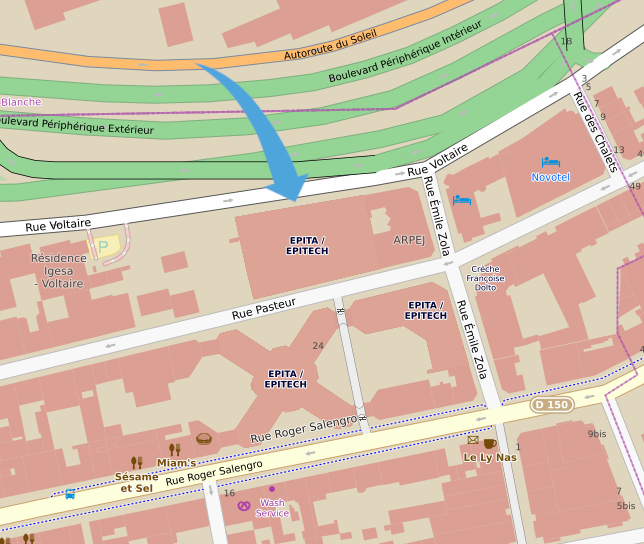
Location
EPITA
14-16 rue Voltaire, 94270 Le Kremlin-Bicêtre
Amphitheater 401, 5th floor
Public transports
Métro 7: Porte d'Italie
Bus 47/125/131/185/186: station Roger Salengro-Fontainebleau
Saturday 6
Introducing the LSE Week
13h55 14h00
Performing open-syscall surgery on SSHd with eBPF as a scalpel - Martin Schmidt
14h00 14h45
eBPF is a revolutionary technology with origins in the Linux kernel that can run sandboxed programs in an operating system kernel. It is used to safely and efficiently extend the capabilities of the kernel without requiring to change kernel source code or load kernel modules. With eBPF, instead of a fixed kernel, you can now write mini programs that run on events like disk I/O, which are run in a safe virtual machine in the kernel.
In this talk we'll see the process of tracing OpenSSHd without debug symbols.
Slides
Rizin: refactoring of the elf plugin. - Alexis Ehret
14h50 15h20The ELF format is an incredibly versatile format due to a lot of loose constraint in the specifications. Those constraints became disadvantages when a tool need to parse an untrusted binary. I will talk about my contribution to the elf plugin in Rizin and the difficulties encounter along the way during the GSoC 2021. Slides
Dodging deadly signal using eBPF - Esteban Blanc
15h30 16h15
Tired of having your process getting killed? Catching SIGINT and SIGTERM is not enough for you? What if you could catch all signals sent to your process? Using eBPF this is now fairly simple without the need of kernel modules nor source code modification.
Follow the story of the development of blocksig, a tool to protect your process of deadly signals
Slides
Blind Date, a journey into Blind ROP exploitation technique - Thomas Berlioz
16h30 17h15Return Oriented Programming is a well-known exploitation technique in the world of pwn. This attack has numerous variations and this is what makes it so powerful. Blind ROP is one of them, and today we will see a CTF application of this fabulous trick. Let me be your guide in this quest for the flag! Slides
How Ocarina of Time 64 was decompiled - Darius Engler
17h20 17h50The goal of this presentation is to introduce the "Ocarina of Time 64" decompilation project. During this presentation I will mostly talk about the technical aspect by explaining first what "matching" decompilation is and what the associated benefits and drawbacks are. I will then talk about the faced difficulties and the tools that were developed for the project. Slides
Rump session
18h00 19h00
- A closer look on the Gameboy system, Clothide Levesque
- Deeply understanding the blink program, Gabriel Jorge
- Site scrapping, Adrien Navratil
Apéro & Barbecue
19h00 00h00
Sunday 7
Adding multi-file support to gccrs, an alternative Rust compiler for GCC - Arthur Cohen
14h00 14h45
The Rust language is a modern system programming language whose compiler rustc relies on the LLVM compiler framework. While LLVM is very recent and capable, it suffers from a lack of architectural target options compared to GCC, a much older and polyvalent compiler framework.
In order to improve the language as well as stabilize its design, an ongoing effort is being made to add Rust support to GCC: gccrs. This compiler is far from complete, and still lacks important features for the Rust ecosystem, such as the handling of projects with multiple source files.
In this talk, we will explore the challenges faced by gccrs as well as the experience and hurdles of contributing to this compiler and adding new necessary Rust features.
Slides
Welcome to the world of Transformers: from moderation to code generation - Pierre Guillaume & Corentin Dûchene
14h55 15h25
Transformers models have been a major breakthrough in many fields starting in Natural Language Processing (NLP). These models were described for the first time in the paper: Attention Is All You Need in 2017.
Therefore, models like BERT/RoBERTa have shown to be really efficient in many NLP classification tasks. In addition, Transformers like GPT-3 (made by OpenAI) have been used for text generation and appears to have impressive results.
In this presentation, we will first describe how Transformers can be used for text moderation in social media and then how these models can be used for code generation tasks.
Slides
Snapshot fuzzing with KVM and LibAFL - Tanguy Dubroca & César Belley
15h30 16h15
Fuzzing is a technique used to automatically find bugs in computer software. There is a wide spectrum of techniques to improve the fuzzing process, and lately all the craze is about snapshot fuzzing.
This talk will explain how we integrated virtualization technologies into the libAFL fuzzing framework to do snapshot fuzzing.
Slides
Developing a Linux driver in Rust for ARM - Esteban Blanc, Arthur Cohen & Martin Schmidt
16h25 17h10
While Linux is not primarily an embedded-focused operating system, it is still used on platforms such as the Raspberry Pi. In the case of these platforms, kernel modules provide a helpful way to interact with various devices at a kernel level, which often communicate using low- level protocols, such as SPI or I2C.
Using Rust for that kind of workloads provides numerous advantages, and while the kernel API for these protocols has been tried and tested for a very long time, there are currently no Rust abstractions available.
In this presentation, we will talk about our ongoing effort to bring an abstraction over the SPI protocol in safe Rust, for Linux, on the ARM64 platform, and how we used it to implement a simple device driver. The talk will draw comparisons against the original implementation in C, which provides the same amount of features. Finally, we will dive into the techniques used and our experience working with Rust-for-Linux.
Slides