LSE Summer Week - July 7 - July 9 2018
Lieu et plan d'accès
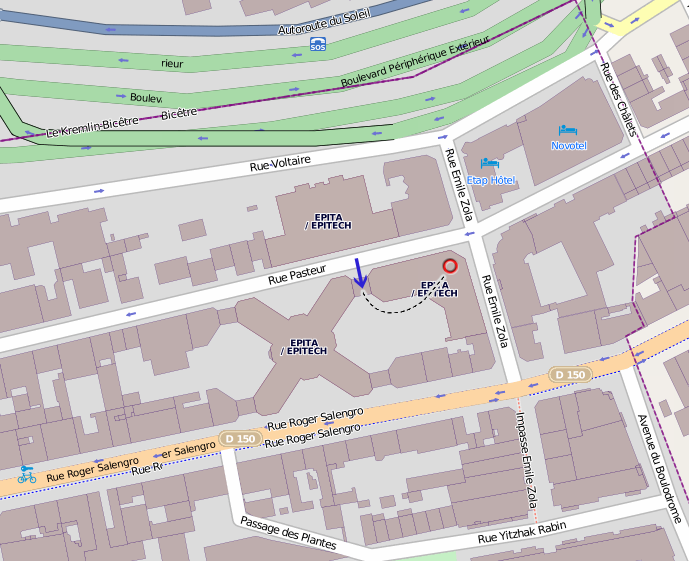
Amphithéâtre 4, EPITA, 24 rue Pasteur, 94276 Le Kremlin-Bicêtre.
Transports en commun : métro 7 (station Porte d'Italie), bus 47/125/131/185/186 (station Roger Salengro-Fontainebleau).
Saturday 7
Introducing the LSE Week
13h55
Epic bug hunt: the longest bug - Marc Espie
14h15 15h00I finally fixed a sporadic bug in OpenBSD's pkg_add. This nasty little bug is known in our circle as "the cups bug". It happened from time to time, and was really frustrating because it seemed completely unpredictable. This is the story of that bug hunt, how I finally instrumented things enough to reproduce it, figure out what was going on, and nailed it to the wall. Most epic bug ever, it "just" took me over 3 years to finally get rid of it. Youtube
Machine Learning and Clusterization of malware at a large scale (with Open Source tools) - Robert Erra
15h15 16h00Malware are now developed at an industrial scale and human analysts need automatic tools to help them. We propose here to present the results of our experiments on this difficult problem: how to cluster a very large set of malware (with only static information) to be able to classify some new malware. All our experiments have been done with code written in Python and we have mainly used scikit-learn so you will probably be able to do the work again with your own feature vector (well we hope for you!). We will present some results on our dataset of two million malwares, we call it our blob. We will give some example of the results we have found and we will talk about future works that could be interesting to do (well: problems still to be solved). Youtube
Troubles with Treble - Alizée Penel
16h15 17h00In Oreo release (Android 8.x), Google re-architected its OS in order to help OEM to speed up their device releases. During this talk, we will detail how Treble refactors Android low layers by adding even more interfaces and IPC. Then, we will highlight its impacts on development and security. Youtube
BitTorrent for iPXE - Victor Collod
17h15 17h45iPXE is a popular network oriented bootloader, which currently isn't able of sharing data it downloads. Adding this feature means greater efficiencies, as well new challenges to overcome. Youtube
Rump Session
18h00 19h00
Barbecue
19h00
Sunday 8
Implementing a clone of OpenBSD pledge into the Linux kernel - Guillaume Pagnoux
14h30 15h00OpenBSD pledge is a nice, easy-to-use mitigation technique that would be nice to be seen under Linux. Let's see what it is, what already exists and how we can implement it using some of the kernel features. Youtube
Edit and continue in GDB - Alexandre Bernard
15h15 16h00Debugging is an everyday game to many developers. Stop, recompile and restart the debugging session are three annoying steps. Let’s see if we can get rid of it in gdb and apply code changes while our program is in break mode. Youtube
Writing a x86_64 hypervisor (canceled) - Thomas Bitzberger
16h15 17h00During this talk, we'll go through the steps of coding a hypervisor from scratch, using Intel virtualization extensions. We'll cover what's needed to launch very simple virtual machines up to running Linux guests in bare metal.
LLVM : Command line replacements for GNU Binutils - Paul Semel
17h15 18h00A lot of GNU binutils have their equivalent in the LLVM project. As the majority of people are already accustomed to the GNU ones, it would be great to make the LLVM binutils command lines compliant. The goal of this project is that people would be able to integrate LLVM tools in their existing toolchains without any efforts, and thus increase the number of projects using LLVM binutils. Youtube
iSCSI and Libvirt - Clémentine Hayat
18h15 18h45iSCSI protocol is famously used for block storage over TCP. Let’s see how the current libvirt implementation allows us to use iSCSI blocks for VM storage, and how we can improve it. Slides
Apéro/bar
19h00
Monday 9
Natural Language Processing and Speech Recognition through Machine Learning - Xavier Cadet
15h00 15h30Natural Language Processing offers many challenges and applications. After an explanation of Natural Language Processing, I will move onto Speech Recognition, and draw an overview of its applications, and state-of-the-art techniques linked to Machine Learning and Deep Learning. Youtube
IP database and port redirection configuration using etcd - Maxence Caron-Lasne
15h45 16h15We will see in this talk how to maintain an etcd database which contains ip addresses and network options of services in a local network, and using it to make this information available on a web page. We will also see how to configure ipvs port redirection using etcd as a configuration backend. Youtube
Vulkanizing Virgl - Nathan Gauër
16h30 17h00Virglrenderer is a project whose goal is to provide OpenGL 3D acceleration to a virtualized guest. Vulkan is a low level, low overhead API. Let's see what is Vulkan, and how to vulkan-ize virgl. Youtube
Text classification using Deep Learning - Antoine Sainson and Hugo Linsenmaier
17h15 17h45Text classification is one of the main tasks in NLP. During this talk, we will present the principal methods used in our classification system during the DEFT 2018 evaluation campaign. We will go through a variety of state of the art techniques focusing on deep learning, in order to classify french tweets. Youtube
Python and Machine Learning: How to clusterize a malware dataset ? - Sébastien Larinier
18h00 18h45The goal of this presentation is to show how to use python to develop a machine learning application. We take examples of security data like malware and we explain how to transform data to use some algorithms of machine learnings. We details the different algorithms, the different librairies of Scikit-learn and Tensorflow. The algorithms help to cluster quickly a (small) database malware to create yara signature for using in Incident Response. After this presentation, participants will be able to work on little dataset and develop some code based on theses librairies and create yara signature. Youtube