LSE Summer Week - July 17 - July 19 2014
Lieu et plan d'accès
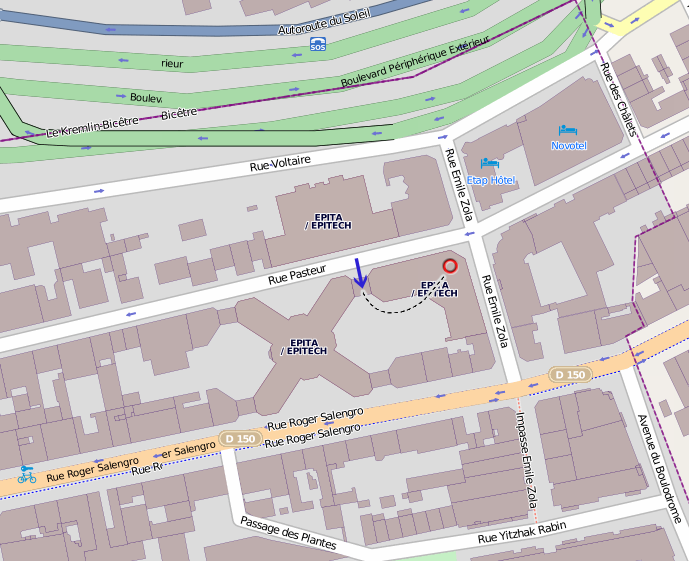
Amphithéâtre 4, EPITA, 24 rue Pasteur, 94276 Le Kremlin-Bicêtre.
Transports en commun : métro 7 (station Porte d'Italie), bus 47/125/131/185/186 (station Roger Salengro-Fontainebleau).
Planning Complet
Playlist
Thursday 17
Introducing the LSE Week
19h00 19h15Discovery of Pyrser - Lionel Auroux
19h15 20h00Pyrser is a full Python 3 parsing module using P.E.G that provides an agnostic DSL to describe your grammars. Pyrser has an unique grammar composition features to inherit new grammar from existing ones. Pyrser also provides a type system module to handle classic static typing and type inference. To understand what Pyrser is capable of, we will go through basic type theory and how you can use Pyrser to add static typing into a DSL with examples. Slides Youtube
Analysis of a door locking system - Pierre Surply & Rémi Audebert
20h15 21h00In this talk we will share what we've learned after installing a rogue controller in the existing electrical system. We then analysed the signal that links the locks and reverse engineered the code of the microcontroller and peripherals. Slides Youtube
Katacryptography: Rise and Fall of cryptography - Robert Erra
21h05 21h50From theory to reality: a walk in the cemetery of your cryptographic algorithms. We propose to present some recent problematic issues in the use of cryptographic algorithms. Slides Youtube
Friday 18
How applications are run on Android? - Jeremy Lefaure & Jean-Loup Bogalho
19h00 19h45A look into Dalvik, the original Android's JVM. What can be improved, and how, by its successor: ART. Slides Youtube
Design and implementation of a RPC library in python - Rémi Audebert
19h50 20h10How to leverage Python's features to create clean, intuitive and powerful API. Slides Youtube
Memory protection on AVR32 - Pierre Surply
20h30 20h50A brief overview of the AVR32 architecture and how to deal with the lack of Memory Management Unit on UC3 microcontrollers. Slides Youtube
Linux file systems - Adrien Schildknecht
21h00 21h45Explaining concepts and major features of modern file systems and how they are implemented in linux Slides Youtube
Saturday 19
Porting and testing a TCP/IP stack in your OS without an ethernet driver - Nassim Eddequiouaq
13h00 13h45A simple way to get a TCP/IP stack working in your kernel, An overview of the current portable solutions (uip, lwip, Bentham's implementation..) followed by an emphasis on lwip implementation and a HOW-TO test it without an ethernet driver. Slides Youtube
Static Program Analysis: The Good, The Bad and The Ugly - Marwan Burelle
13h50 14h35Static program analysis is a long running story in theoretical computer science. Unfortunately, it has long been restricted to languages with well founded semantics, far from real-life programming languages. Increasing needs for security and safe applications have push the domain to evolve and leave the cozy but unrealistic proof of program field, into a more useful (but less accurate) approach. This talk will present some background on the domain and proof-of-concept useful analysis. Slides Youtube
An overview of the LFH - Bruno Pujos
14h50 15h35Explaining how the heap allocation and in particular the Low Fragmentation Heap works in Windows and the security mechanisms introduced by Microsoft in order to hardening the exploitation. Discussing the heap exploitation techniques and how their difficulty has increased since Windows XP. Slides Youtube
GPU on KVM - Gabriel Laskar
15h40 16h25What are the current status of gpu support on KVM ? A brief exploration of gpu support on virtualization. Slides Youtube
Reverse engineering AT32UC3A's JTAG - Pierre Surply
16h40 17h25JTAG's IEEE 1149.1 is a widely used interface to test printed circuit boards. Initially designed for boundary scan, it is also used today to access non-standard On-Chip Debugger features like program counter monitoring and breakpoints control. This talk will explain how this interface works and will focus on AT32UC3A microcontroller to explain how to reverse-engineer device specific JTAG features. Slides Youtube
Initramfs and a glimpse of the module loader in stos - Paul Hervot
17h35 17h55A short introduction on stos' module loading features used by the commandline, followed by a presentation of initramfs' implementation. Slides Youtube
Binary compatibility: many ABI provided by a single kernel - Emmanuel Dreyfus
18h10 18h55We will study the binary compatibility framework provided by the NetBSD kernel to support binaries built for other systems. First we will focus on the Linux case: foreign binary matching, specific system call table, system call translation, signal handling, performances and limits of binary compatibility. We will then have a look at binary compatibility with MacOS X. Slides
OpenBSD news: package signing and more - Marc Espie
19h00 19h45With the 5.5 release, the whole of OpenBSD is now signed, which of course includes packages. The tools (pkg_add) were already signature-ready a few years ago, but the advent of a simple signing tool (signify, courtesy of Ted Unangst) gave it some momentum. Here's a look at what's new in pkg_add in 5.5, specifically what goes on under the hood, and the shape of things to come. This will also go back to design specifics, and how this fits within the general philosophy of OpenBSD. Slides Youtube